- “OPSEC — An Out of Body Experience,” a dynamic and informative presentation on the principles of Operations Security (commonly referred to as OPSEC), that includes an overview of the five-step analytical OPSEC process. ForensIQ’s own Tom Mauriello, the former Director of the US Department of Defense, Interagency OPSEC Support Staff (IOSS), explains how OPSEC can and should be integrated into all operations to provide effective protection of critical and proprietary information. OPSEC is being implemented throughout the national and homeland security communities as a planning methodology vital to the success of securing homeland assets. Mr. Mauriello also discusses the mission of the IOSS that acts as a consultant to all U.S. government departments and agencies, and contractors sponsored by the U.S. government, having a national security mission. OPSEC is more than a program – it is a state of mind. It focuses on the protection of critical, but unclassified information that becomes advantageous in the hands of the adversary. If you believe that you already understand OPSEC, or you have never heard the term before, you will benefit from this awareness training.
- PRESENTATION TIME: 60 to 90 minutes.
- NUMBER OF PARTICIPANTS: No maximum number within a single event. Video-teleconferencing included in a single event is additional.
INTENDED AUDIENCES:
- Federal, state and local government agencies having national security missions and/or having security awareness requirements.
- Any organization having sensitive or intellectual data to protect.
- Public Interest Groups.
2. OPSEC and Analytic Risk Management Training Courses — On January 22 1988, President Ronald Reagan signed National Security Decision Directive (NSDD) 298, establishing the National OPSEC Program. It states that each Executive department and agency assigned or supporting national security missions (Including DoD contractors) with classified or sensitive activities shall establish a formal OPSEC program. ForensIQ can provide OPSEC courses as needed including the following categories of training:
- OPSEC Fundamentals
- OPSEC Analysis
- OPSEC Program Management
- OPSEC and Web Risk Assessment Course
- Analytic Risk Management
3. Counterintelligence and Counterterrorism Training — ForensIQ has established partnerships with CT/CI Training Partners, LLC, Global Counterterror and Counterintelligence Training Solutions,http://ctcitraining.org; and Ray Semko: D*I*C*EMAN, Defense Information To Counter Everything (DICE) that is a threat to your organization, presented in a high-impacted briefing by security expert Ray Semko,http://www.raysemko.com/.
ForensIQ’s Tom Mauriello spent 30 years as a security and counterintelligence special agent for the US Department of Defense. The one common denominator in all his assignments during those years was developing and presenting security and counterintelligence and awareness training at hundreds of events, educating thousands of people in the national security community. His association with CT/CI Training Partners and The D*I*C*EMan is no accident. He has been collaborating with these experts in the security and counterintelligence throughout his career. Now the best of the best is available to those customers who need nothing less.
Contact ForensIQ to discuss your requirements and you will be directed to the training products that best meets your needs.
4. Obtaining Fingerprints Training
- History and Development of Fingerprints
- Recognizing Classification Patterns
- Rolling and Inking Fingerprints
- Evaluating Acceptable 10 finger print cards
- Familiarization of FBI Automated FP System (AFIS)
This workshop trains personnel responsible for obtaining fingerprints during U.S. government clearance processing. The training is a combination of lecture and practical exercises providing each student with the knowledge and skills to obtain acceptable fingerprints for evaluation.
PRESENTATION TIME LENGTH: 4 hours
NUMBER OF STUDENTS: MAX OF 10 STUDENTS
5. Critical Thinking for the Investigator and Security Professional —This training event increases the quality of investigator’s and security professional’s critical thinking skills. The “learning objectives” are to…
- use critical thinking techniques to provide structure to investigative interviews, reporting and decision making;
- integrate the 8 Elements of Thinking and the 9 Intellectual Standards for effective decision making when collecting information;
- construct clear and concise questions; and
- identify when all the questions are answered.
Humans live in a world of thoughts. We accept some thoughts as true. We reject others as false. But the thoughts we perceive as true are sometimes false, unsound, or misleading. And the thoughts we perceive as false and trivial are sometimes true and significant. The mind doesn’t naturally grasp the truth. We don’t naturally see things as they are. We don’t automatically sense what is reasonable and what is unreasonable. Our thought is often biased by our agendas, interests, and values. We typically see things as we want to. We twist reality to fit our preconceived ideas. Distorting reality is common in human life. It is a phenomenon to which we all unfortunately fall prey.
“Each of us views the world through multiple lenses often shifting them to fit our changing feelings. In addition, much of our perspective is unconscious and uncritical and has been influenced by many forces – including social, political, economic, biological, psychological and religious influences. Social rules and taboos, religious and political ideologies, biological and psychological impulses, all play a role, often unconscious, in human thinking. Selfishness, vested interest and parochialism, are deeply influential in the intellectual and emotional lives of most people.” [The Foundation for Critical Thinking – Dr. Linda Elder and Dr. Richard Paul]
As investigators and security professionals, we must take rational command of our cognitive processes in order to rationally determine what to accept and what to reject. In short, we need standards for thought; standards that guide us to consistent quality thinking; standards we can count on to keep our thinking on track; to help us mirror in our minds what is happening in reality; and to reveal the truth with clarity, focus and impact.
This course is presented in three formats:
- A two hour presentation that demonstrates an awareness and need for critical thinking for all professionals. This format is for large audiences in an auditorium type event with no minimum number of participants.
- A four hour workshop that also teaches how and when to use the 8 Elements of Thinking and the 9 Intellectual Standards, and uses several cases studies for group participation during the workshop. This format allows a maximum of 40 participants with lecture and limited group discussions.
- A full two to three day course that requires prerequisite homework before in class lecture and real case group exercises. This format has a maximum of 30 participants with a significant amount of group discussions and presentations.
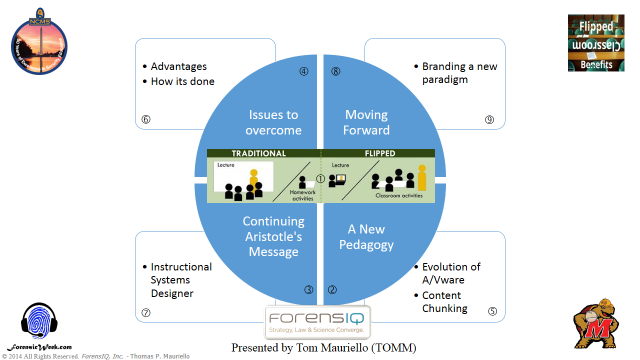
6. “The Flipped Classroom – Turning Your Security Education Program Upside-down” – This keynote address was first presented by Tom Mauriello at the NCMS 50th Annual Seminar, June 18, 2014, Gaylord National Resort & Convention Center, National Harbor, Maryland. The term “Flipped Classroom” has become something of a buzzword in the last several years in the academic community. In essence, “flipping the classroom” means that students or briefing participants gain first exposure to new material outside of the classroom or briefing room, usually via readings, videos, YouTube clips and use of other forms of communication. This is followed by their presence in the classroom or briefing room to do the harder work of assimilating the knowledge through problem-solving exercises, group discussions, or debates. This is not the way we have done business in the past, but “times… they are a changing.” This keynote presentation highlights the “whys” and “hows” this is happening right under our noses, as we blend the techniques of the past and present with the technologies and excitement of the future.
PRESENTATION TIME – 30 to 60 minutes
Mindmap Overview of Flipped Classroom Presentation
See all participants survey comments while evaluating Tom Mauriello’s presentation at the NCMS 50th Annual Seminar, June 18, 2014. Click here Mauriello_Survey_2014_NCMS
Read what NCMS New England Members said about Tom Mauriello’s presentation.NCMS NE Chapter Newsletter_Sep2014